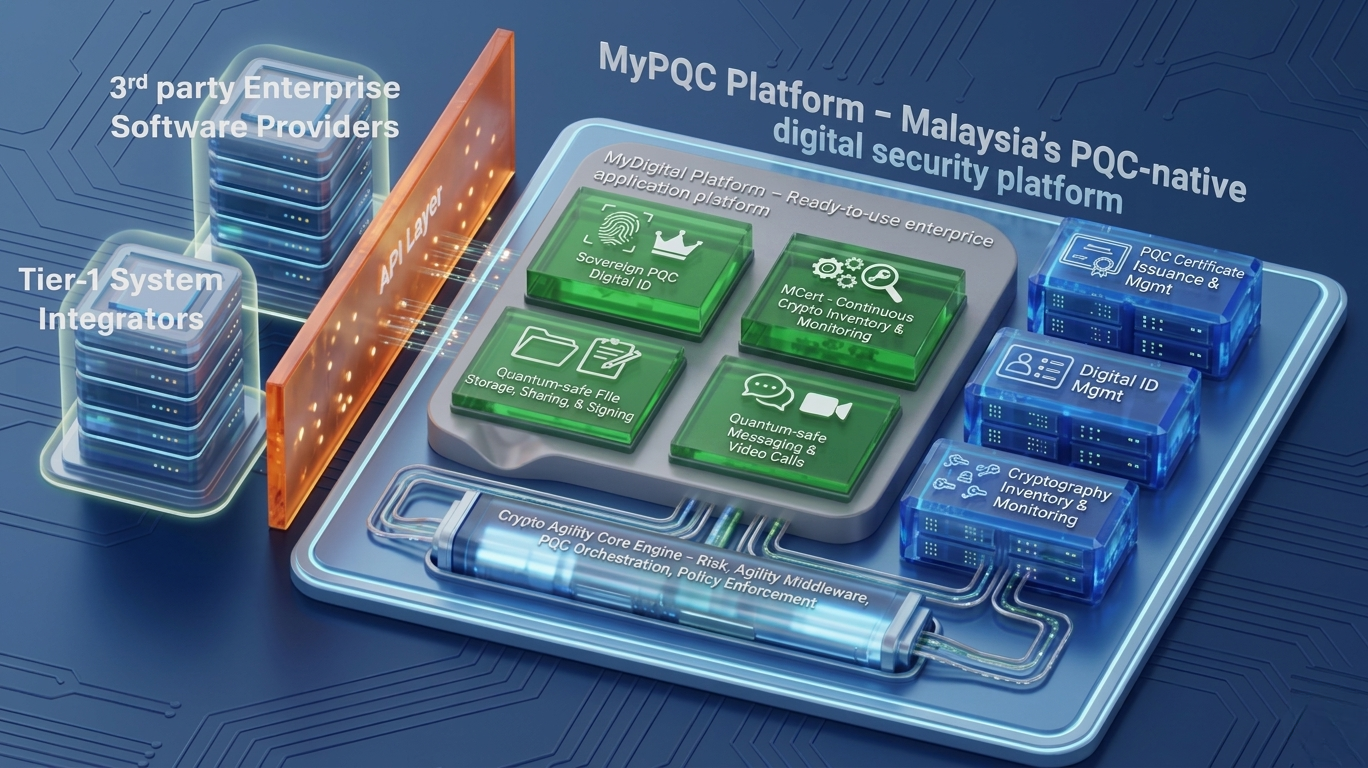
The MyPQC Platform: A Post Quantum Cryptography certified Platform.
Three layers, one platform: ready-to-use applications, cryptographic services you can build on, and a crypto-agility core engine that powers the whole platform. Each layer plugs cleanly into the next — all accessible through a single API layer.